Cyberwar Without War: How States Fight Without Crossing Red Lines
The rapid expansion of computing and communications technologies and the ongoing improvement in the performance of computerised systems have created a new space. Cyberspace, a space created not by nature but by human agency, presents both significant opportunities and considerable risks, including unpredictable ones. Given its relatively recent emergence, spanning no more than four decades. A comprehensive understanding of cyberspace and its implications is still in its early stages.
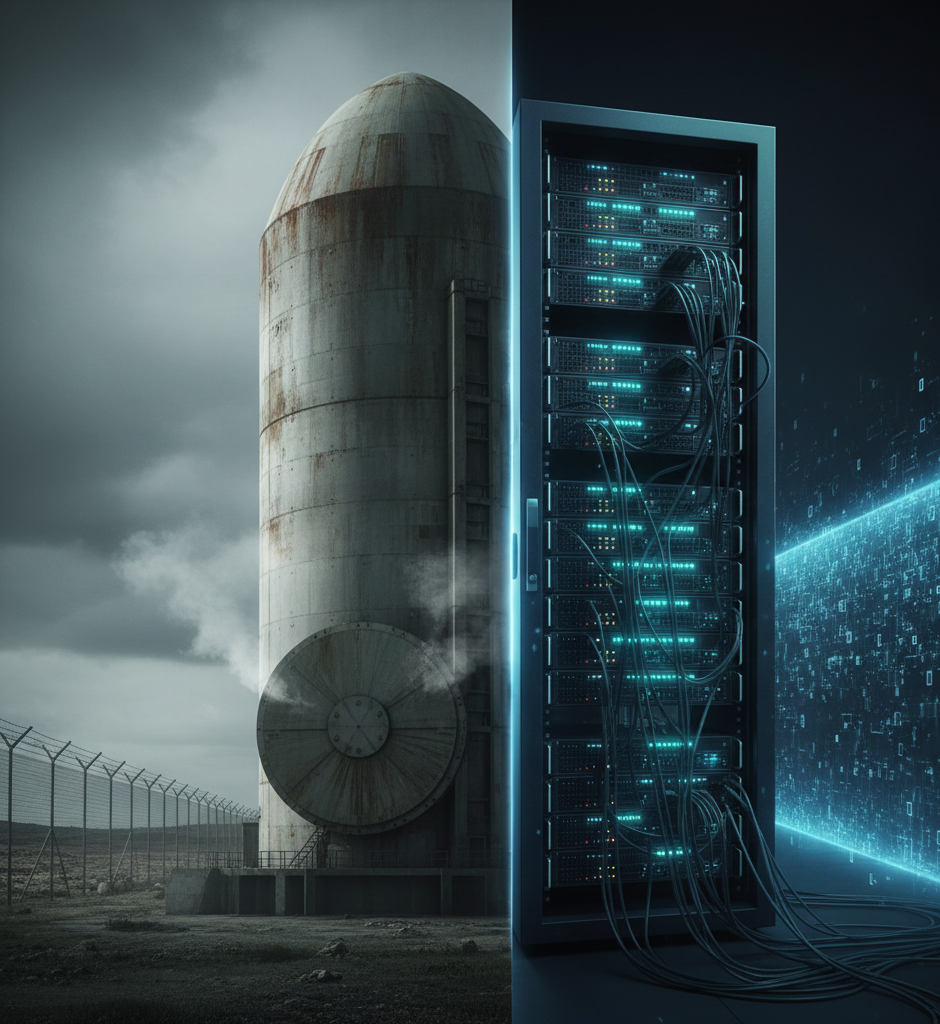
Throughout history, warfare has evolved through multiple generations, each marked by significant technological and strategic shifts. The first generation is typically associated with the Napoleonic era, while the second generation emerged after the Industrial Revolution, characterised by increased firepower and linked to the First World War. The third generation saw further advances in firepower, reflecting the era of the Second World War. The fourth generation introduced the rise of non-state actors and insurgencies, fundamentally altering the nature of conflict. Today, the evolution has reached the domain of cyberwarfare, following a progression from pikes and muskets to nuclear weapons and digital attacks.
The fifth and current generation is characterised by cyberwarfare. Cyberwar involves digital attacks primarily aimed at espionage and at targeting adversaries' strategic and tactical structures. The primary objectives include stealing valuable information, such as military data, or disrupting government servers.
The term 'cyber' derives from the Greek word 'kybernetes,' meaning 'one who steers or governs.' Cyberwarfare embodies the concept of 'fighting without fighting,' as articulated in Sun Tzu’s The Art of War. By shifting conflict from the physical and kinetic realm to the digital domain, nations can achieve strategic objectives, paralyse adversaries, and inflict economic damage without engaging in traditional warfare. This shift creates a grey area that enables states to claim plausible deniability, allowing them to inflict harm without direct physical engagement.
There are seven recognised types of cyberwarfare: espionage, sabotage, denial-of-service attacks, attacks on electrical power grids, propaganda, economic disruption, and surprise cyberattacks.
Each of these methods is intended to challenge, disrupt, and inflict damage upon adversaries. Beginning in the 1980s, the rapid expansion of computer networks and their integration into critical systems fundamentally altered the security landscape, heightening concerns about foreign espionage and information vulnerability. Strategic analysts began to conceptualise digital infrastructures as instruments of conflict, particularly as alternatives to large-scale conventional and nuclear warfare. By the 1990s, the concept of cyber conflict expanded to include non-state actors, reflecting the widespread diffusion of technological capabilities and the increasingly decentralised nature of digital threats.
What are the distinguishing features of Cyberwarfare compared to Traditional Warfare?
Advances in technology and interconnectivity have significantly reduced the likelihood of conventional warfare. Cyberwarfare transcends national borders, constituting a virtual and continuous conflict that blurs the distinctions between civilians and military personnel, peace and war, and state and non-state actors. Unlike traditional warfare, which features defined front lines, cyberattacks target infrastructure, data, and society as a whole, making the entire world a potential digital battleground.
A central challenge in cyberwarfare is attribution. In conventional warfare, the identity of belligerents is typically clear through uniforms, flags, and territorial incursions. In contrast, cyber operations are frequently routed through multiple intermediaries, obscuring the origin of attacks and complicating efforts to assign responsibility. This uncertainty undermines deterrence mechanisms, as effective responses depend not only on the scale of harm but also on confidence in attribution.
Cyber conflict further obscures the boundary between military and civilian domains. Contemporary societies depend on interconnected digital systems that support both national security and civilian activities. Consequently, cyber operations often target or affect infrastructure serving dual purposes, challenging the traditional separation between combatants and non-combatants that is foundational to international humanitarian law.
Another significant distinction involves proportionality and escalation control. In conventional warfare, the use of force typically follows an observable spectrum, enabling adversaries to gauge intent and respond appropriately. In contrast, cyber operations vary widely in both impact and visibility, making it difficult to determine whether an action constitutes espionage, coercion, or an act of war. This ambiguity heightens the risk of miscalculation, as states may interpret the same action in fundamentally different ways.
Finally, cyberwarfare is noted for its persistence rather than decisiveness. Traditional wars frequently aim at territorial control, military defeat, or political capitulation. Cyber conflict, by contrast, tends to favour continuous engagement, erosion of trust, and long-term strategic pressure over rapid or conclusive outcomes. This shift demonstrates a broader transformation in how power is exercised, emphasising influence, disruption, and uncertainty rather than direct conflict, ambiguity, and plausible deniability in cyber conflict. Malicious cyberattacks, which do not rise to the level of force under international law, pose a significant problem for the international community. Attributing responsibility for malicious cyberattacks is imperative if states are to respond and prevent them from continuing.
Unfortunately, due to both technical and legal issues, attributing malicious cyber-attacks to the responsible state or non-state actor is difficult, if not impossible, in the vast majority of attacks. Even if an injured state may recursively trace the malicious cyber-attack to the responsible IP address, this is not enough under the current international customary law to hold a state or non-state actor responsible for the cyber-attack, as it is virtually impossible to bridge the air gap between the computer system and end user to demonstrate affirmatively who initiated the attack. Even if a state could demonstrate the identity of the end user who initiated the attack, this is not enough to link the end user to the state for the purpose of assigning responsibility under existing customary international law.
The Rise Of Cybersecurity As a National Security Concern
This is not only a byproduct of technological development but also a reflection of the expanding role of intelligence agencies in society and the covert dimension of statecraft. Indeed, the ubiquity of information technology augurs a new golden age of espionage. Cyberspace is essential for military operations and policing, to be sure, but this reflects the prominence of intelligence in modern warfare and law enforcement. Cybersecurity matters for non-state actors, too, in no small part because rms and individuals find themselves on the receiving end of foreign intelligence services.
Actors do not conduct cyber operations for their own sake but rather in pursuit of a political or economic goal within a social system of other actors with their own goals. The political problem is evaluating the costs and benefits of conducting the operation, given the expected reactions of other affected actors. Both problems must contend with uncertainty, and different participants may be more or less able to manage them.
Any organisation that uses a computer is a potential target for cyber operations, so long as a competitor can imagine a use for its data. Many people are left alone in cyberspace, despite being vulnerable, simply because they are not wealthy or valuable enough to attract attention. States may use cyber espionage for many purposes: to gather information on national security threats and to gain insight into foreign decision-making to support military targeting and operations, to advance the competitive position of domestic firms, to influence or intimidate civilian populations, to monitor and track dissidents, to steal or extort financial resources, etc. The same organisation, moreover, might be targeted for quite different reasons. Cyber operators might penetrate a foreign firm to steal its intellectual property or to obtain its negotiating positions to benefit their own firms. With an unfair commercial advantage, they might target the same firm to indirectly learn about a government’s policies through the firm's communications with government officials, or to gain access to technologies that enable follow-on espionage operations.
Identifying the actual perpetrator of a cyber-attack is notoriously tricky. Sophisticated state actors use proxies, intermediate servers, and masked code to provide "plausible deniability". Because military retaliation requires high certainty of attribution to a specific state, acting on insufficient or suspected evidence could lead to an unlawful, retaliatory attack against the wrong target.
Attribution uncertainty is not simply a flaw in cybersecurity; it is a feature they exploit. Plausible deniability operations include Attribution uncertainty, which is not merely a weakness in cybersecurity; it is a feature deliberately exploited by state actors. Plausible deniability operations often involve using proxies, such as patriotic hackers or criminal organisations, to carry out attacks, thereby enabling states to credibly deny involvement. Ambiguity allows a state to project greater power than it may actually possess. When a victim suspects a powerful adversary but lacks definitive proof, caution remains essential, as it can enhance the perceived strength of the attacker. Even if attribution is eventually established, the attacker may still benefit. Leaders use attribution uncertainty to maximise the political advantages of an attack while minimising risks, enabling operations within a 'grey zone' where responsibility remains ambiguous—scalability, and reversibility. Unlike traditional military forces, cyber operations can be calibrated with precision, adjusted rapidly, and withdrawn without the lasting physical damage associated with kinetic conflict. This pliability makes cyber tools especially suitable for managing competition below the threshold of war, where the objective is not decisive victory but sustained leverage.
Crucially, cyber operations are embedded within wider national strategies rather than deployed as isolated acts of aggression. They complement diplomatic, economic, informational, and military instruments of power, strengthening an all-encompassing approach to statecraft. In this context, cyber capabilities indirectly weaken adversaries by exploiting system-wide vulnerabilities rather than confronting their military strength directly.
Furthermore, cyberwar questions traditional conceptions of violence and legitimacy in international relations. Although conventional force is governed by visible escalation and accepted conventions, cyber operations operate in a space where legal and normative frameworks are persistently underdeveloped. This allows states to pursue tactical goals while avoiding the political costs associated with overt military action.
Ultimately, cyberwar represents a transformation in the exercise of power within the international system. It emphasises persistence over shock, influence over destruction, and calculated ambiguity over tactical clarity. Therefore, cyber operations should be viewed not as acts of battlefield violence, but as ongoing instruments of state strategy designed to shape the conditions of competition in a digitally networked environment.
Legal Grey Zones: International Law and Cyber Conflict
Cyber operations occupy a "legal grey zone" in international law, frequently intended to fall just below the threshold of an "armed attack" as defined in the UN Charter. While states are increasingly using cyber operations to target critical infrastructure, such as electric grids and communications systems, these actions rarely justify direct military retaliation due to challenges in legal interpretation, attribution, and the high risk of escalation.
According to international law, specifically Article 51 of the UN Charter, a state may only use force in self-defence if an "armed attack" occurs. The prevailing legal view, supported by the ICJ's Nicaragua judgment, is that an act must have a "scale and effects" comparable to a conventional kinetic attack (resulting in death, injury, or significant physical destruction) to qualify as an armed attack. Many cyber operations, even destructive ones, fail to meet this high bar, leaving them classified as violations of sovereignty or prohibited interventions rather than as direct triggers for war.
Cyber operations are primarily used in grey-zone warfare—a space between peace and war—to achieve strategic, non-kinetic objectives (paralysis, espionage, economic interference) without triggering an immediate, overt military backlash.
Article 2(4) of the UN Charter prohibits the threat or use of force against the territorial integrity or political independence of any state. A cyber-operation that breaks a power grid or disrupts government services may violate this article, but that does not automatically authorise a kinetic, military answer under Article 51.
While a single minor, low-level cyber-attack rarely justifies war, some argue that the "accumulation of events" theory allows states to aggregate multiple, minor incidents over time to claim that a cumulative, threshold-crossing "armed attack" has occurred.
Critical Infrastructure and Civilian Vulnerabilities in Cyberwarfare
Cyberwarfare against critical infrastructure, specifically electric grids, communication networks, and financial systems, constitutes a paradigm shift in modern conflict, allowing states and non-state actors to exert "pressure without bombs." By exploiting digital vulnerabilities, these attacks can cause physical destruction, economic disruption, and severe civilian panic, effectively turning civilian infrastructure into a primary non-kinetic target.
Power networks represent the most critical targets, as their disruption affects all other infrastructures. Attacks have evolved from data theft to targeting Industrial Control Systems (ICS) and Supervisory Control and Data Acquisition (SCADA) systems. Disrupting telecommunications impairs emergency services and public communication. Attackers also target banks, stock exchanges, and payment systems to induce financial panic, disrupt daily life, and steal funds. The convergence of Information Technology (IT) and Operational Technology (OT) has expanded the attack surface, frequently exposing legacy equipment that was not originally designed with security considerations in mind.
"Pressure Without Bombs": Tactics and Impacts of Cyberwarfare- Ransomware-as-a-Service: Criminal groups regularly target critical infrastructure, with some operating under the, perhaps implied, protection of nation-states.
Wiper malware permanently deletes data and destroys systems, rather than just locking them for ransom. Physical Damage via Digital Means can directly cause physical equipment, like circuit breakers, to fail, as demonstrated by the Aurora vulnerability, which could cause generators to explode. Social Disruption is the ultimate goal of breaking popular confidence and inciting fear without a direct military invasion.
Rationale for State Preference for Cyberwarfare Over Open Conflict
States increasingly prefer cyberwarfare over open conflict because it better aligns with the organisational constraints of the contemporary international system. In an era distinguished by economic interconnectedness, nuclear deterrence, and heightened political costs of war, cyber operations offer a means of competition that preserves strategic pressure without triggering catastrophic escalation.
At its core, cyberwar enables states to pursue political aims while staying below the threshold of armed conflict. Classic warfare carries unequivocal legal, moral, and diplomatic consequences, often forcing states into rigid escalation pathways once violence begins. Cyber operations, by contrast, exist within a grey zone where intent, attribution, and proportionality are inherently ambiguous. This vagueness allows states to test limits, signal resolve, and impose costs without committing to irreversible action.
Cyberwarfare also eases the risks associated with military miscalculation. Open conflict relies on visible deployments of force and kinetic exchanges that can rapidly spiral beyond political control. Cyber operations, while not risk-free, afford greater flexibility and reversibility, enabling states to modify their behaviour in response to adversary reactions. This malleability makes cyber tools especially suitable for managing long-term rivalry rather than seeking decisive confrontation.
Furthermore, cyberwar complements existing deterrence structures rather than undermining them. Within systems where the threat of overwhelming retaliation constrains direct military confrontation, cyber capabilities provide an alternative channel for exerting influence. Rather than replacing traditional military power, cyberwar extends the strategic toolkit accessible to states operating under conditions of mutual restraint.
Finally, the preference for cyberwar demonstrates a broader transformation in the exercise of power. Contemporary competition emphasises endurance, influence, and systemic disruption over geographical conquest or battlefield victory. Cyber operations are well-suited to this environment, allowing states to mould perceptions, undermine confidence, and exploit institutional vulnerabilities over time.
Taken together, cyberwar offers states a form of strategic engagement that maintains a balance between pressure and restraint. It enables sustained competition in a context where open conflict has become increasingly costly, unpredictable, and politically unsustainable. As such, cyberwarfare is not a temporary substitute for classic warfare, but a structural adaptation to the realities of modern international politics.
The Evolving Nature of Warfare in the Digital Era: Cyberwarfare signifies a fundamental change in how states pursue power, influence, and security in the modern international system. Rather than replacing traditional forms of warfare, it reflects an adaptation to a strategic environment in which political, economic, and deterrence-based limitations increasingly constrain open conflict. In this context, cyber operations offer a means of sustaining competition without incurring the full costs of war.
The strategic appeal of cyberwar is found in its ability to operate amid ambiguity. By fuzzing the boundaries between peace and conflict, cyber operations allow states to pursue objectives incrementally, shaping adversary behaviour while avoiding clear escalation thresholds. These questions established frameworks of international law and deterrence, forcing a review of how aggression, responsibility, and proportionality are understood in the information age.
At the same time, cyberwar stresses the persistence of classical strategic principles. Political objectives continue to guide conflict, restraint remains central to rational state behaviour, and power is exercised through influence rather than destruction. What has changed is the domain through which these principles are expressed. Cyberspace has become a critical arena where competition unfolds continuously, often invisibly, and without definitive resolution.
Ultimately, cyberwarfare highlights the developing character of conflict rather than its disappearance. As states seek to manage rivalry amid mutual vulnerability, cyber operations will remain a central feature of global politics. Understanding cyberwar not as an anomaly, but as a planned response to contemporary constraints, is essential for grasping how power will be contested in a progressively interconnected world.
References-
Arquilla, J., & Ronfeldt, D. (1993). Cyberwar is coming! RAND Corporation.
Arquilla, J., & Ronfeldt, D. (1996). The Advent of Netwar. RAND Corporation.
Betz, D. J., & Stevens, T. (2011). Cyberspace and the State: Toward a Strategy for Cyber-Power. International Institute for Strategic Studies.
Buchanan, B. (2020). The Hacker and the State: Cyber Attacks and the New Normal of Geopolitics. Harvard University Press.
Clausewitz, C. von. (1976). On War (M. Howard & P. Paret, Eds. & Trans.). Princeton University Press. (Original work published 1832)
Gray, C. S. (2013). Making Strategic Sense of Cyber Power: Why the Sky Is Not Falling. Strategic Studies Quarterly, 7(2), 3–40.
Kello, L. (2017). The Virtual Weapon and International Order. Yale University Press.
Libicki, M. C. (2009). Cyberdeterrence and Cyberwar. RAND Corporation.
Nye, J. S. (2017). Deterrence and Dissuasion in Cyberspace. International Security, 41(3), 44–71.
Rid, T. (2013). Cyber War Will Not Take Place. Oxford University Press.
Singer, P. W., & Friedman, A. (2014). Cybersecurity and Cyberwar: What Everyone Needs to Know. Oxford University Press.